Mark your calendars:
October 21, 2026
— see you there!
The Longest-running IT Security Festival in Central & Eastern Europe is going to be held in Budapest at
Lurdy Conference and Event Center.
Speakers and attendees are coming from all around the world to exchange information about the latest trends in cybersecurity.

<What_is_hacktivity?/>
The most anticipated IT Security event in the region
#HACKTIVITY is the biggest event of its kind in Central & Eastern Europe. About 1000 visitors are coming from all around the globe every year to learn more about the latest trends of cybersecurity, get inspired by people with similar interest and develop themselves via presentations and comprehensive workshop sessions.
<Conferenc_updates/>
Latest News
-
Where the Cybersecurity Community Meets, Hacks, and Connects in the cyber month in Europe
Hacktivity, Central and Eastern Europe’s longest-running hacker and IT security festival, returns on 21 October 2026 with an expanded format…
-
Hacktivity Workshops: Registration Is Live!
The wait is over. Hacktivity Workshops are officially unlocked, and you can grab your spot right now. This isn’t your…
-
The CEE Region’s Premier IT Security Festival Returns and Announcing Speakers
Hacktivity 2025: The CEE Region’s Premier IT Security Festival Returns and Announcing Speakers <Updated_28.07.2025/> 📍 Budapest, 3 October 2025 –…
-
Hacktivity 2025 Tickets Now Live!
Hacktivity, the longest-running IT-security and hacker festival in Central & Eastern Europe, has officially opened ticket sales for its 2025…
Archives
Preserving the Pulse of Tech: Insights That Endure

PRESENTATIONS
3 tracks and 1 days 40+ hours of presentations highly technical topics

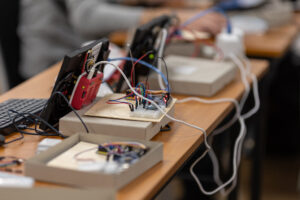
WORKSHOPS
2 hours long comprehensive sessions great variety of subjects

HACKCENTER
exchange ideas learn new skills solve challenges

NETWORKING
social interaction among people with similar interes
The Story of Hacktivity
It started in 2003 when a group of security experts were looking for a forum to meet and exchange experience. Since then each year the number of participants has doubled at the oldest independent Hungarian event.
Since 2010 Hacktivity has been a fully international event with all programmes held bilingually. In 2010 1,000, in 2011 and 2012 1,200, in 2013 1300 participants including official and alternative information security experts, students and teachers from universities and colleges offering IT degrees, professional organizations from the countries of three continents (Czech Republic, Slovakia, Poland, Romania, Serbia, France, Germany, Portugal, Korea, USA, India, Hungary) attended the two-day event. The conference received never-before-seen media coverage with television crews ranging from the state television of the People’s Republic of China through French television channel AFP to Al-Jazeera and almost a dozen other channels shooting on the conference location.
At the 2,000 sqm conference venue live demo presentations are held in 3 sections along with Hello workshops, exhibitions, book presentations and games to make the programme diverse. The professional day is completely free of marketing content. Candidates must apply to be among the speakers selected by the programme committee on the basis of professionalism, experience and leading knowledge. Our sponsors (whose number is continually on the rise) are present at the event in a unique way through stands, games and special entertainment programmes.
<Thoughts_on_Hacktivity?/>
What Our Speakers Said
“
“
“
“
“
“
<all_about_security_and_networking/>
The IT Security Festival in Central & Eastern Europe
Topics of the conference